You’re online reading this, so it’s safe to assume you don’t live under a rock. That means you’ve already heard about the WannaCry ransomware attack sweeping across the globe like faster than the clap in WWI. The virus travels through nefarious links, emails, and file-sharing programs, quickly spreading across corporate networks and other shared systems. Once a computer is infected, it’s files are encrypted, and users are instructed to make a payment—typically via BitCoin—of $300 in order to unlock their files.
This isn’t the first ransomware attack, and it won’t be the last, but the origin, scope, and some of the outcomes of the WannaCry attack make it special. Here are a few of the fun facts you may not know about WannaCry. Think of it as a little light reading while you wait for the world to end.
1. Yes, WannaCry Originated at the NSA
A hacking group called the ShadowBrokers released a bunch of stolen NSA documents back in April, including the code for a Windows vulnerability exploit dubbed EternalBlue.

The NSA guys figured out how to hijack Windows’ file-sharing backbone to sneak in and move around computers and networks, ShadowBrokers brought it to the world, and pairing it with the encryption/ransomware code gives us WannaCry (and now, several WannaCry derivatives).
2. And Yes, Microsoft Probably Could Have Stopped This Sooner
Not only has Microsoft known that the vulnerability was public knowledge since the beginning of April, but according to the Financial Times [warning: hard paywall], Microsoft has actually had a patch available for the vulnerability for some time. And if you paid for their ongoing support for your Windows XP machine, you would likely have been protected. They’ve now released the patch for free, but it only protects against the initial infection—it won’t do you any good if WannaCry has already made its way into your computer.
If you were running Windows 10 and had performed a system update since March, you were already protected. Many businesses and individuals are still using XP, though, and many others just don’t update that regularly. It turns out those annoying reminders are actually sort of important.
3. Kill-Switch Found, Kill-Switch Activated, Kill-Switch Killed
Shortly after news of the outbreak broke, a white hat who goes by the handle MalwareTech was researching the bug, and accidentally-on-purpose found a kill-switch that dramatically slowed WannCry’s (Also called WannaCrypt) progress. You can read a detailed breakdown of his process here. In short, the virus would try to communicate with an unregistered domain so the hackers behind the attacks could verify that the virus was running properly on non-quarantined machines, (i.e. machines that don’t belong to cool bros like MalwareTech, who purposefully used the virus in virtual/sequestered environments in order to learn about and defeat it).

MalwareTech registered the domain name being used to verify the viral operation, and this ended up not only thwarting the automated verification but actually halted the spread of the virus…for a time. New versions of WannaCry have already been released that don’t use the unregistered URL trick and that don’t have a kill-switch, so though MalwareTech helped keep things at bay for a minute the floodgates have reopened.
4. WannaCry Brought More Chaos Than Profit
Shutting down systems like Britain’s National Health Service, FedEx, and Spanish telecom giant Telefonica brought WannaCry the attention of international media, and so far the virus has infected at least 250,000 computers in more than 150 countries. But current estimates say the original WannaCry attack has netted the hackers behind it less than $100,000, and the next best copycat has earned less than half that.
Don’t get me wrong: close to six figures for a week of sitting back and watching the world burn seems like a sweet salary package at times. But given how hard the hammer will come down if these guys are ever found, I think I’d probably pass.
5. BlackBerry’s Making Out Like a Bandit
BlackBerry smartphones were the gold standard in cybersecurity for years, and are still the phone of choice for many government employees and other security-sensitive folks. This has literally nothing to do with the WannaCry attacks for two reasons. First, the attacks only affect Windows computers, and second, BlackBerry is no longer involved in manufacturing hardware at all (though they have licensed the BlackBerry name for phones made and sold in certain Asian markets).
And yet, BlackBerry’s stock shot up 10% when news of the attacks broke, and it’s hovered at the same price for the past week. Go figure.
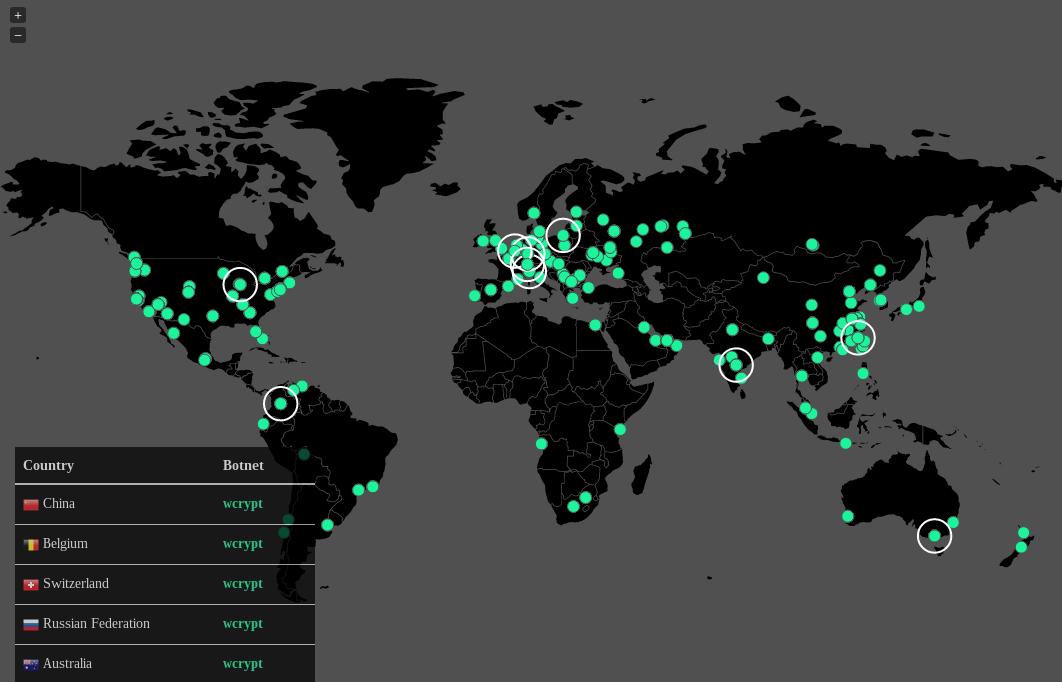
6. You Can Watch WannaCry Get To Work in Real Time
Hat tip to MalwareTech, yet again, who not only helped to slow the spread of WannaCry but who also helped document it. You can watch, too. It’s weirdly and perhaps unbelievably fascinating.
7. There May Be Hope
Law enforcement and security experts say that though the temptation to pay may be high, you shouldn’t do it. There’s the public good to think about—more people paying means more attacks are likely in the future—and if that doesn’t do it for you, there’s this: when you pay up, the hackers know who you are, they know you pay, and they’re more likely to target specifically you later on.
But don’t give up hope! If you have an infected XP machine and you haven’t rebooted since receiving the attack, there’s a fix on GitHub that might get you unlocked for free. Maybe. But at least it’s something. Next time, keep that computer updated and consider running an OS that isn’t older than the concept of a smartphone.

